If your business uses any AI-powered tools — whether for content generation, customer automation, data analysis, or workflow orchestration — the current situation with Langflow deserves your direct attention. CISA has added CVE-2026-33017, a critical code injection vulnerability in the Langflow AI framework, to its Known Exploited Vulnerabilities catalogue, based on confirmed evidence of active attacks already under way. This is not a theoretical warning. CISA’s Known Exploited Vulnerabilities list exists specifically to document flaws where exploitation in the real world has been verified. If a vulnerability makes that list, someone is already using it.
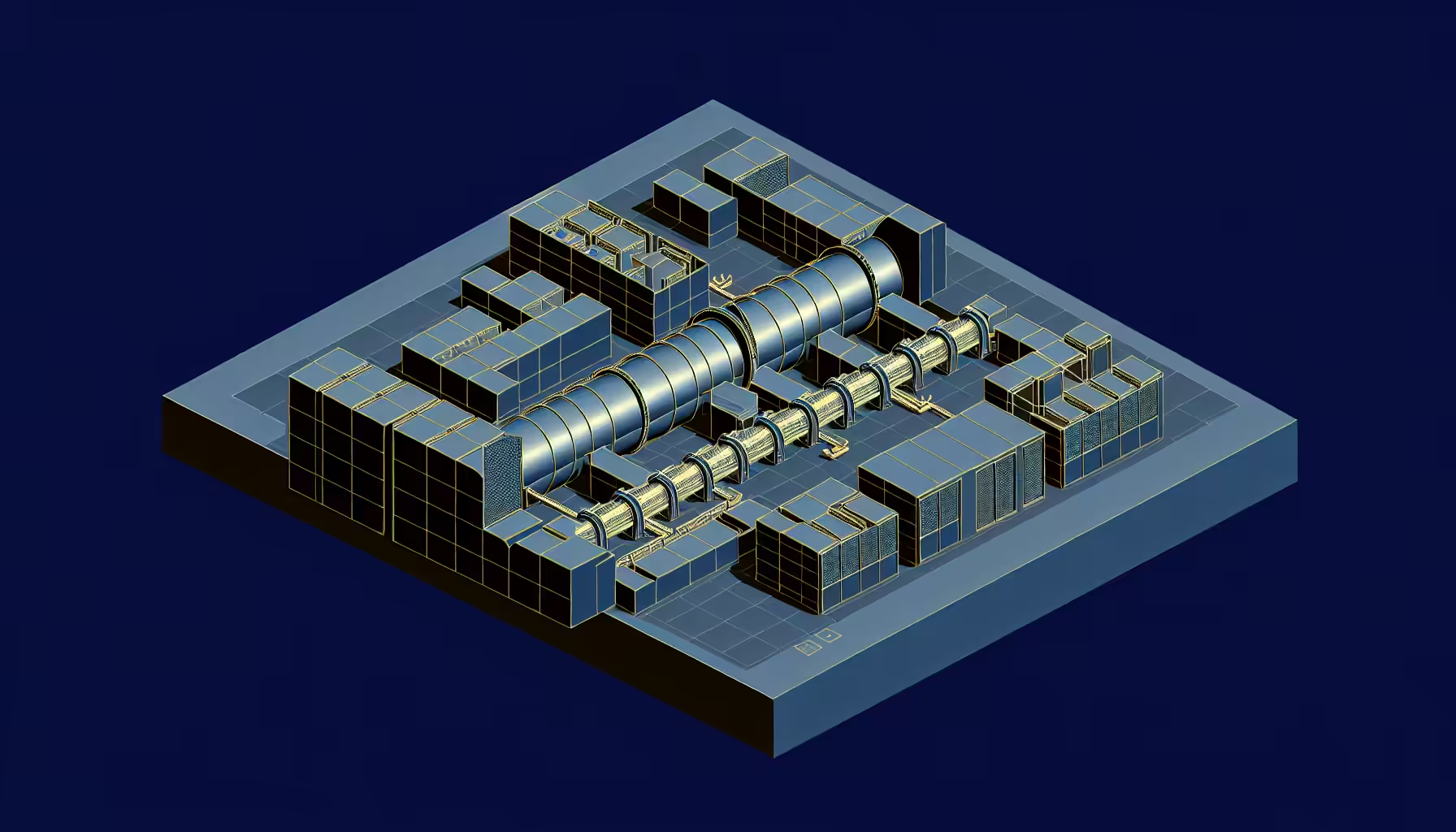
Langflow is an open-source framework used to build and manage AI workflows — the kind of visual, modular tooling that businesses and development teams increasingly rely on to connect large language models, data sources, and automation pipelines. Its popularity makes it an attractive target. The vulnerability stems from an exposed API endpoint and is linked to three distinct weaknesses: improper control of generated code, improper evaluation of injected directives, and missing authentication for critical functions. In plain terms, an attacker who finds this endpoint does not need a password. They can inject and execute their own code directly.
The consequences of that are serious. A compromised Langflow instance does not just expose one tool in isolation. AI workflow frameworks like this typically connect to databases, cloud services, third-party APIs, and stored credentials. An attacker gaining entry through an unpatched endpoint can move laterally through your infrastructure, exfiltrate sensitive data, and potentially seize control of cloud environments tied to your business operations. Sysdig has advised organisations not to expose Langflow directly to the internet, to monitor outbound traffic carefully, and to rotate API keys, database credentials, and cloud secrets if suspicious activity is detected. That last point matters: by the time you are rotating credentials reactively, the damage may already be done.
Federal agencies in the United States were ordered to patch affected systems by 8 April 2026, and CISA has explicitly advised private sector companies, state and local governments, and other non-federal entities to treat that deadline as a benchmark for their own response. That guidance applies regardless of where your business is based. The internet does not have national borders, and attackers targeting vulnerable Langflow deployments are not limiting themselves to American organisations.
Speed of Exploitation Is the Real Story Here
What makes this incident particularly instructive for executives is the timeline. A previous critical Langflow vulnerability, CVE-2025-3248, scored 9.3 out of 10 and was weaponised within 20 hours of public disclosure. Twenty hours. That is not enough time to convene a board meeting, brief your IT team, and draft a remediation plan. It is barely enough time to become aware of the problem, let alone act on it. CISA warned of active exploitation of that earlier flaw in May 2025, with attackers able to achieve unauthenticated remote code execution via the same category of exposed API endpoint. The fact that Langflow is now appearing in CISA’s catalogue for a second time is a clear signal that this framework is under sustained, deliberate scrutiny from threat actors.
The lesson here is not specific to Langflow. It applies to any internet-facing tool in your digital estate. AI integrations, automation platforms, form processors, CRM connectors, and the plugins layered on top of your WordPress environment all carry the same category of risk when left unpatched or exposed without proper access controls. The security posture that protects your core website needs to extend to every tool connected to it. A well-maintained WordPress installation sitting behind a compromised AI workflow tool offers very little real protection, because the attacker is already inside your broader infrastructure.
What Business Owners Should Do Now
The response to this kind of incident does not require technical expertise from you personally, but it does require you to ask the right questions of whoever manages your digital infrastructure. Start here:
- Audit what AI and automation tools are connected to your business systems. Many organisations have accumulated integrations — workflow tools, AI assistants, API connections — without a complete picture of what they are or where they sit.
- Confirm that all tools are running current, patched versions. Outdated software is consistently the most common point of entry in attacks of this type.
- Ensure that no AI workflow tools or development frameworks are directly exposed to the public internet without authentication controls in place. If something does not need to be publicly accessible, it should not be.
- Establish a process for acting on security advisories quickly. A twenty-hour exploitation window means that monthly patching cycles are not sufficient for high-risk tools. Your team needs a faster response mechanism for critical vulnerabilities.
- Review cloud credentials and API keys associated with any AI tools. If you are uncertain whether your Langflow deployment or any similar tool has been accessed without authorisation, treat credential rotation as a precautionary baseline, not an overreaction.
The rapid adoption of AI development tooling has outpaced the security practices surrounding it in many organisations. That gap is exactly what attackers are exploiting. The Langflow situation is a timely and concrete illustration of how quickly a disclosed vulnerability becomes an active threat — and how much is at stake when the affected system sits at the centre of your AI and automation infrastructure. If you would like a structured review of your WordPress environment and the tools connected to it, get in touch with me directly. This is precisely the kind of audit that should be on your agenda now.